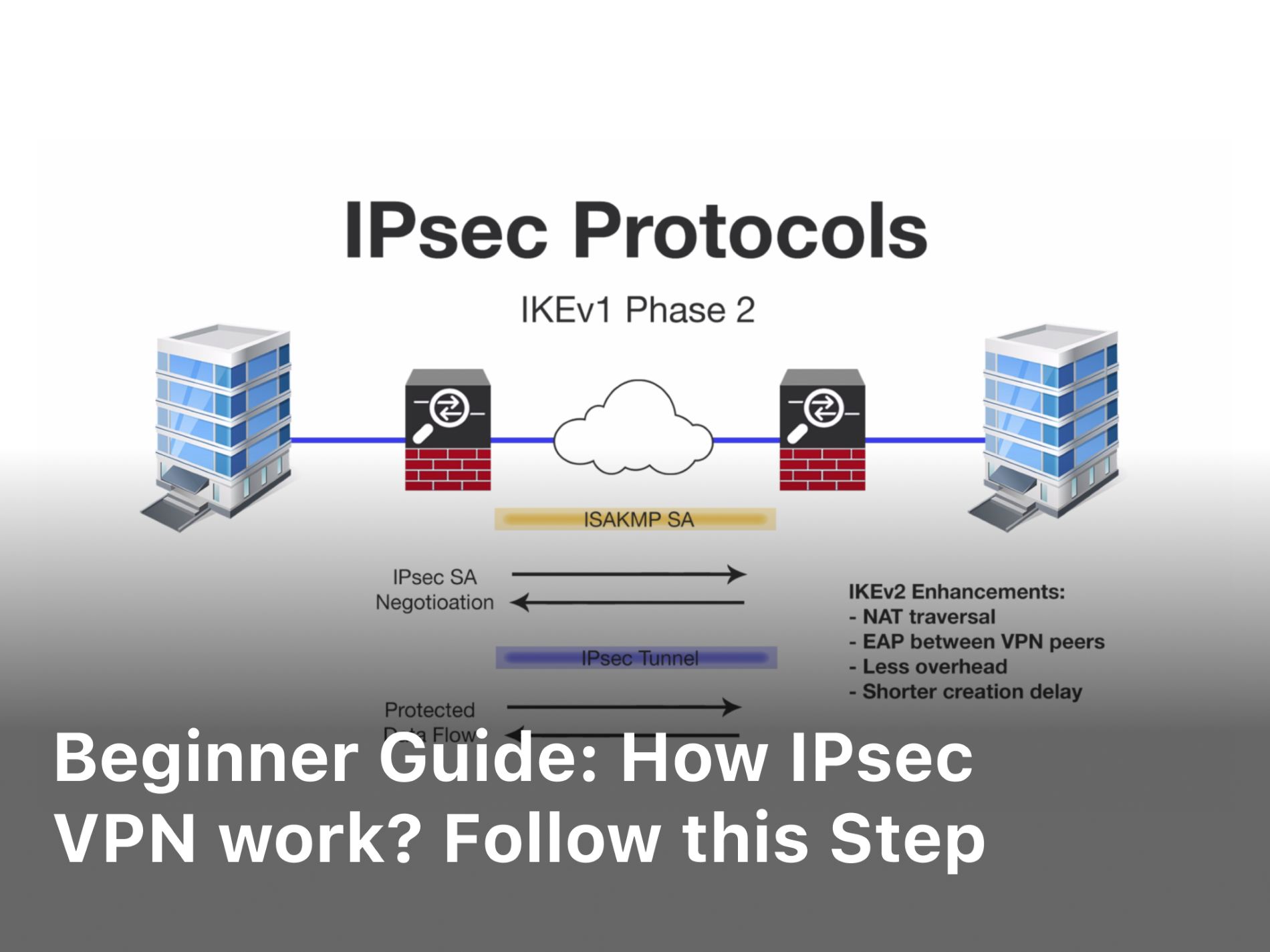
As a newcomer to the world of virtual private networks, understanding how IPsec VPNs function and are configured can seem like a daunting task. However, by following this step-by-step guide, you will gain a foundational knowledge of IPsec VPN in no time. We will start from the basics by defining what IPsec is and how it establishes secure connections over the Internet. You will then learn about the two main protocols that make IPsec work: Internet Key Exchange (IKE) and Encapsulating Security Payload (ESP). With the fundamentals in place, we will walk through how to set up your own IPsec VPN on Windows and macOS as well as on iOS and Android mobile devices. By the end, you will have a solid understanding of how IPsec VPNs operate and the ability to implement one on your own. Let’s get started.
What Is IPsec VPN and How Does It Work?
To understand IPsec VPN, you must first understand what a VPN is and how it works. A virtual private network or VPN securely connects two networks over an insecure network like the internet. An IPsec VPN uses the IPsec protocol to encrypt and authenticate each IP packet in a data stream.
IPsec VPNs can operate in two modes:
- Transport mode encrypts the IP payload but leaves the IP header untouched. This mode is used between two hosts.
- Tunnel mode encrypts both the IP header and the IP payload. This creates a VPN tunnel between two IPsec gateway devices to protect an entire IP subnet. Tunnel mode is more commonly used in commercial VPNs.
How IPsec VPN work and by implementing cryptography through the use of cryptographic algorithms and keys to encrypt and decrypt IP packets. The two main protocols used are:
- Authentication Header (AH) which authenticates IP packets.
- Encapsulating Security Payload (ESP) which encrypts and authenticates IP packets.
ESP is more commonly used since it provides both authentication and encryption. The encryption algorithms used include AES and 3DES. For authentication, hash algorithms like SHA-1 and SHA-2 are used.
Keys are exchanged between the two IPsec endpoints using an Internet Key Exchange (IKE) protocol. Pre-shared keys or RSA signature based certificates can be used to authenticate the IKE exchange.
By following these steps, an IPsec VPN can securely and privately connect two networks over the internet through encrypted tunnels and authentication, allowing remote users and networks to communicate in a safe manner.
IPsec VPN: PSK vs PKI
To secure your VPN connection, you’ll need to choose between a pre-shared key (PSK) and public key infrastructure (PKI). Each has its advantages and disadvantages to consider:
PSK:
- Uses a shared secret passphrase to authenticate users. Simple to set up but less secure.
- Anyone with the passphrase can access the network. Difficult to revoke access.
- Limited to a single passphrase for all users. Does not scale well.
PKI:
- Uses digital certificates to authenticate users and encrypt data. More complex to implement but more secure.
- Certificates are unique to each user and device. Easier to revoke access if needed.
- Scales well for large deployments with many users.
- Requires a certificate authority (CA) to issue and manage certificates. Additional complexity.
For small teams with limited resources, a PSK-based VPN may suit your needs. However, for enterprise-level security and scalability, PKI is superior. Some solutions offer a hybrid model, using PSK for some connections and PKI for others based on your risk assessment.
In summary, evaluate your security requirements and resources to determine which authentication method is right for your organization. A PSK can work for simple needs, but for robust protection of sensitive data and systems, the enhanced security of PKI is worth the additional investment in time and infrastructure. With the right design and management, a PKI-based VPN can deliver strong security and an improved user experience.
IPsec VPN Configuration: Policies and Proposals
To configure IPsec VPN, you first need to define the policies and proposals. These determine how the IPsec tunnel is secured between the VPN devices.
VPN Policies
A VPN policy defines the source and destination subnets between which the IPsec tunnel is established. It also specifies the IPsec proposal to use to secure the tunnel. On each VPN device, configure a policy with the local source subnet, remote destination subnet, and chosen IPsec proposal.
IPsec Proposals
An IPsec proposal specifies the encryption and authentication algorithms to use for the IPsec tunnel. You configure proposals on each VPN device with the following options:
- Encryption algorithm: Choose an algorithm like AES (Advanced Encryption Standard) or 3DES (Triple Data Encryption Standard). AES is faster and more secure.
- Encryption key length: For AES, choose 128, 192 or 256 bit. Longer is more secure but slower.
- Authentication algorithm: Choose an algorithm like SHA1 (Secure Hash Algorithm 1) or SHA2 (SHA256, SHA384 or SHA512). SHA2 is more secure.
- Authentication method: Choose between pre-shared key (PSK) or public key infrastructure (PKI). PSK uses a shared secret key. PKI uses certificates for authentication which is more scalable and manageable.
- Diffie-Hellman (DH) group: Choose a DH group for exchanging encryption keys. Higher groups are more secure but require more CPU power. Choose a group based on your VPN device capabilities.
Once the policies and proposals are configured on both VPN devices, they can negotiate an IPsec tunnel using the parameters you specified. Make sure the policies and proposals on each device are compatible, with at least one common proposal, for successful tunnel establishment. Modify as needed if there are any negotiation failures.
Following these steps will allow you to configure secure IPsec VPN tunnels between your sites. Be sure to also configure additional options like tunnel monitoring, VPN interfaces and routing. Let me know if you have any other questions!
Configuring IPsec VPN on Routers, Firewalls and Endpoints

To configure IPsec VPN on network equipment and endpoints, you will need to go through the following steps:
Configure the VPN gateway
The VPN gateway is the router, firewall or server through which VPN connections are made. Log into your VPN gateway and navigate to the IPsec or VPN configuration page. Here you will define the VPN connection by entering parameters like:
- VPN type (select IPsec VPN)
- Gateway IP address
- IPSec mode (tunnel mode is typical)
- Encryption and authentication algorithms (AES, SHA-1, etc.)
- Perfect Forward Secrecy (PFS) setting
- Pre-shared key
Be sure to choose strong encryption and authentication algorithms for the best security. Generate a pre-shared key that is at least 20 characters long, containing a mix of letters, numbers and symbols.
Define network access
You will need to specify which local networks will be reachable through the VPN. This includes entering network IP addresses and subnet masks for the private networks behind the VPN gateway. These parameters define what the remote VPN client will have access to.
Related Article : Access Public Wi-Fi with VPN! Here’s why
Install VPN software
On endpoints like laptops, desktops and mobile devices, you will install VPN client software to connect to the VPN gateway. The software may be provided by your VPN gateway vendor or from a third party. Install the software on each device that needs to connect to the VPN.
Configure the VPN client
Open the VPN client software and enter the IP address or hostname of your VPN gateway. You will also enter the pre-shared key that matches the key defined on the VPN gateway. Additional parameters may include the username and password for the VPN gateway, if authentication is enabled.
Connect and test
With the VPN gateway and clients configured, you can now initiate a VPN connection from an endpoint. If the connection is successful, test access to a private network resource to confirm the VPN is working properly. Monitor your VPN gateway and endpoints for any connectivity or security issues.
Troubleshooting Common IPsec VPN Issues
If you encounter issues with your IPsec VPN, there are a few common troubleshooting IPsec VPN steps you can take to resolve them.
Check VPN Server Status
First, verify that the VPN server is up and running properly. Log in to your VPN server and router to check for any error messages or irregular connectivity statuses. Ensure all cables are properly connected and restart the VPN server if needed.
Confirm VPN Client Settings
Double check that your VPN client settings on the connecting device are configured correctly. The parameters like VPN server address, authentication method, and encryption algorithm should match what is set up on the VPN server. Any mismatches in these configurations will prevent a successful connection. It may be helpful to delete the VPN profile and recreate it to ensure all settings are correct.
Test Connectivity
Try to connect to the VPN from another device to determine if the issue is specific to one client device or affects all connections. If other devices are able to connect successfully, the settings or software on the problematic device may need to be reconfigured or updated. You can also try connecting to the VPN from an alternate network location to rule out any local network problems.
Check Firewall Settings
If you are still unable to connect, firewalls on the VPN server, client device, or network equipment could be blocking the connection. Double check that the necessary ports and protocols for IPsec VPN are allowed, including UDP port 500 for IKE and IP protocol 50 for ESP.
Reset Router or Access Point
As a last resort, you may need to reset your router, access point, or other network equipment to factory default settings to correct any software issues before reconfiguring the VPN settings from scratch. Be aware that this will disrupt connectivity for any other devices on the network as well.
With patience and persistence, you can resolve most common IPsec VPN connectivity problems. However, for ongoing or complex issues, it may be best to contact your network administrator or VPN service provider for further help.
In conclusion, this beginner’s guide has shed light on the functioning of IPsec VPNs, providing a clear understanding of their operations. By following the step-by-step instructions presented here, you can confidently set up and utilize an IPsec VPN to enhance your online security. IPsec VPNs play a crucial role in encrypting and protecting your internet traffic, ensuring the confidentiality and integrity of your data. By implementing these security measures, you can browse the web with peace of mind, knowing that your online activities are shielded from prying eyes. Take control of your privacy and safeguard your digital presence with IPsec VPNs today.